Financial Metrics Study on 4126047013, 5017906455, 6985984236, 18772555923, 11842, 4012525314
The Financial Metrics Study examines selected unique identifiers, including 4126047013 and 5017906455, to evaluate their financial health through key ratios and profitability metrics. This analysis highlights significant trends and performance indicators, offering a comprehensive view of each entity’s financial standing. Understanding these metrics is crucial for stakeholders, as they inform strategic decisions. The implications of these findings raise important questions about transparency and accountability in the financial ecosystem, inviting further exploration.
Overview of Unique Identifiers
Unique identifiers serve as essential tools in financial metrics analysis, enabling the accurate tracking and management of entities within the financial ecosystem.
Their identifier significance lies in promoting data integrity, ensuring that each entity is distinctly recognized.
This clarity fosters transparency and facilitates informed decision-making, empowering stakeholders to navigate the complexities of financial data with confidence and autonomy, ultimately enhancing operational efficiency.
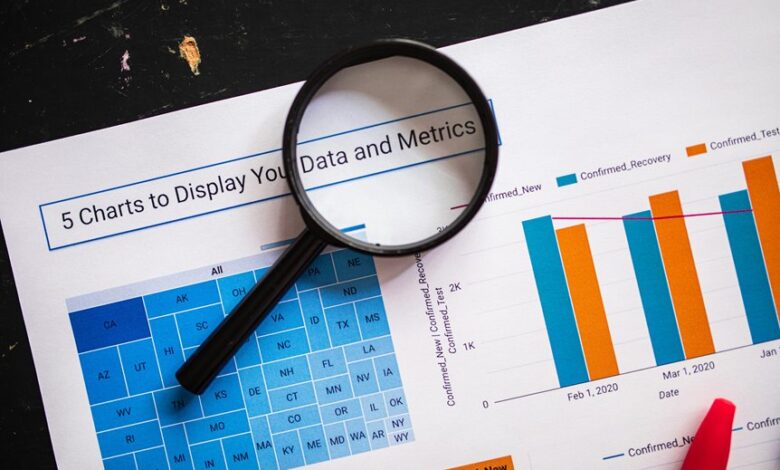
Key Financial Metrics Analysis
While understanding the financial landscape is crucial for informed decision-making, a thorough analysis of key financial metrics provides insights that drive strategic initiatives.
Financial ratios, such as return on equity and profit margins, offer a clear view of organizational health.
A detailed profitability analysis enables stakeholders to assess performance, identify growth opportunities, and make data-driven choices that enhance overall financial freedom and sustainability.
Trends and Performance Indicators
Analyzing trends and performance indicators provides a deeper understanding of financial health beyond static metrics.
By examining financial trends over time, one can discern patterns that influence performance evaluation. This analysis reveals the dynamics of revenue growth, cost management, and profitability, enabling stakeholders to make informed decisions.
Ultimately, recognizing these trends fosters a proactive approach to financial strategy and resource allocation.
Implications for Stakeholders
Understanding the implications of financial metrics for stakeholders is crucial, as these insights directly influence strategic decisions and investment opportunities.
Enhanced stakeholder engagement fosters collaboration and trust, while financial transparency ensures accountability.
Stakeholders benefit from clear metrics that guide their understanding of performance, risk, and potential returns, empowering them to make informed choices that align with their interests and aspirations.
Conclusion
In conclusion, the Financial Metrics Study on the specified unique identifiers reveals critical insights into their financial health and performance trends. As the adage goes, “a stitch in time saves nine,” emphasizing the importance of timely data analysis for stakeholders. By leveraging these findings, stakeholders can make informed decisions that enhance transparency and accountability, ultimately fostering sustainable growth and stability in the financial ecosystem. The analysis underscores the necessity of continuous monitoring and evaluation of financial metrics.



